

Firefox, hiredis, Strace updates in Tumbleweed
Snapshots of openSUSE Tumbleweed this week have been frequent with a fair amount of software packages arriving in each snapshot..
Among some of the packages to update this week were Vim, libsoup, libzypp, strace and more.
A cool 13 packages arrived in snapshot 20231101. An update of dracut was among those that arrived. The initial ramdisk tool addresses issues related to PKCS11, dracut’s version handling, Bash compatibility, network device naming and more. An update of gnome-text-editor 45.1 improves proper entity tags for comparing documents after a “Save As” operation. The package also fixes row styling in preferences and addresses a memory leak issue with GtkNativeDialog. An update of hxtools 20231101 makes changes such as adding compression .zst suffix support for the qtar tool to eliminate unnecessary lines in spec files. An update of poppler 23.10.0 makes several core improvements like updating type 3 fonts for Cairo 1.18’s Application Programming Interface and fixes a crash issue with malformed files. The build system enhancements make certain dependencies soft-mandatory and adds support for more gpg releases. Updates of yast2-trans, selinux-policy 20231030, gpgme 1.23.1 and more arrived in the snapshot.
The Halloween snapshot wasn’t too scary with a large amount of Common Vulnerabilities and Exposures being crushed in snapshot 20231031. With the 10 updated software packages, Mozilla Firefox 119.0 addresses a significant amount of CVEs. Solving CVE-2023-5721 was significant as the fix prevents a click-jacking attack, which could trick users into unintentionally interacting with browser prompts and dialogs by improving the activation delay. The release includes fixes for cross-origin size and header leakage, cookie character issues and takes care of 10 other CVEs. The browser also requires Mozilla Network Security Services (Mozilla NSS) 3.94 for its functionality, which arrived in snapshot 20231029. Plasma users should know that KDE integration has been reactivated with updated patches for improved compatibility. The gnu-unifont-fonts 15.1.04 update includes larger supersets of Plane 2 and Plane 3 glyphs in both the default and Japanese versions of the font. Notable changes in the ncurses 6.4.20231021 in the update include the use of oldxterm+sm+1006 in virtual terminal emulator-2014, default configuration changes for “opaque” and “widec” options, and the package has some minor cleanup of the compiler and manpage warnings. The command-line tool qpdf updates to version 11.6.3 and includes tweaks to improve handling of files between 2 GB and 4 GB in size. The tool also has a fix for a data loss bug that could discard characters after escaped octal strings with fewer than three digits. The bug was introduced in qpdf between versions 10.6.3 and 11.0.0. The 6.6 version of the diagnostic, debugging and instructional userspace package strace introduces a new --kill-on-exit option, which sets PTRACE_O_EXITKILL to all tracee processes and prevents them from running after the tracer exits. This option is automatically activated when using -seccomp-bpf without the -p/--attach option. There were also several new syscall decodings and constant updates have been implemented in this release. Thunar 4.18.8 improves the file manager to allow it to guess the correct display to use and fixies critical issues related to unset GNOME Input/Output (GIO) attributes. Shadow 4.14.2 and a few other packages updated in the snapshot.
The 20231030 snapshot introduces support for GL_EXT_texture_shadow_lod and GL_NV_displacement_micromap extensions with the glslang 13.1.1 update. The package also adds a new --no-link option and removes a previously merged patch related toCMake and resource limits. The hiredis 1.2.0 package, which is a C library that provides a minimalistic and easy-to-use client for the Redis database, includes the addition of various features for the sdevent adapter, the ability to specify the keepalive interval and a RedisModule adapter. The package also provides a helper for setting the TCP_USER_TIMEOUT socket option and includes bug fixes for improved stability and functionality. The vulkan-loader 1.3.268.0 update introduces the addition of the VK_LOADER_LAYERS_ALLOW environment variable and includes support for the Debug extension in the test layer; the changes enhance the Vulkan loader’s functionality for managing layers and extensions in Vulkan applications. The vulkan-tools 1.3.268.0 was the last package to update in the snapshot and enhances the capabilities of the Vulkan tools for graphics and compute applications.
The 20231029 snapshot had a fair amount of packages updates. The glib2 2.78.1 package addresses various bug fixes and improvements. It fixes the file truncation issues with ` g_file_set_contents_full()` , resolves build errors and ensures proper file handling. The package also includes enhancements like preserving microseconds for access/modify times. The open-source HTTP client/server library libsoup 3.4.4 brings improvements in HTTP/2 performance, particularly when there is significant buffering. The package adds support for building the libnghttp2 implementation as a subproject, which enhances the capabilities of the library for handling HTTP requests and responses. The second update of the week for libstorage-ng updates the package to version 4.5.155. This update includes changes like merging a specific GitHub issue and extends the testsuite. The update mozilla-nss 3.94 updates prepares the Tumbleweed release for a later update and improves handling string literals, and other adjustments to improve the library’s functionality and security. The update of php8 8.2.12 addresses issues like memory leaks, type errors, and segfaults in the core components. The update also enhances performance, exception handling and content detection in various PHP modules and functions. The vim 9.0.2078 update includes numerous bug fixes and improvements. The text editor addresses issues related to type aliases, Vim9 support, text change triggers and more. The package enhances security measures, improves file recognition and resolves various document-related issues in the snapshot. Other package updates were also in the snapshot and the xfconf version was downgraded to version 4.18.1, which was upgraded to version 4.18.2 a day earlier in snapshot 20231028.
Snapshot 20231028 updates the Linux Kernel. The 6.5.0 kernel-source version bringing improvements such as Bluetooth enhancements and fixes related to ice, KVM, and x86. Advanced Linux Sound Architecture codecs wcd938x also received updates to address runtime Package Manager imbalances and resource leaks. The libstorage-ng 4.5.154 update enhances error reporting in SystemCmd, adds test cases and makes more use of the new SystemCmd interface, along with other minor enhancements and fixes. An issue with the timer library was resolved with thelibzypp 17.31.23 update. An update of openssl 3.1.4 fixes key and IV resizing issues and improves cryptography performance. The xfconf package for the Xfce desktop environment updates to version 4.18.2 and brings various enhancements that were downgraded in the following snapshot.


Updating GNOME shell extensions to GNOME 45

The new version of the GNOME desktop was released more than one month ago. It takes some time to arrive to the final user, because distributions should integrate, tests and release the new desktop, and that's not something simple, and it should integrate in the distribution release planning.
So right now, it's possible that there's just a few people with the latest version of the desktop right now, just people with rolling release distros or people using testing versions of mayor distributions.
This is one of the reasons because a lot of gnome-shell extensions aren't updated to work with the latest version of GNOME, even after a few months, because even developers doesn't have the latest version of the desktop and it's not something "easy" to install, without a virtual machine or something like that. Even if the update is just a change in the metadata.json, there should be someone to test the extension, and even someone to request this update, and that will happen once the mayor distributions release a new version.
I'm using Tumbleweed, that's a rolling release and GNOME 45 is here just after the official release, but of course, a lot of extensions are not working, and in the infamous list of non working extensions there where the three that I'm maintaining right now:
- mute-spotify-ads, extension to mute the spotify app when it's playing ads.
- calc, a simple calculator in the alt+F2 input.
- hide-minimized, hide minimized windows from alt+tab and overview.

The correct way
The correct way to maintain and update a gnome-shell extension should be to test and update "before" the official release of GNOME. It should be something easy for me, using Tumbleweed I can just add the GNOME Next repository, install the new desktop when it's in beta stage, and update the extension there.
But that's something that require an active maintainership... And right now what I do is to update the extensions when they are broken for me, so just when I need them, and that's after I get the new desktop and I find some time to update.
I know that's not the correct way and this produces a bad experience for other people using the extensions, but this is the easier thing to do for me. Maybe in the future I can do it correctly, and provide a tested update before the official release, maybe using snapper to be able to go back to stable, without the need of using virtual machines.
Update your extension to GNOME 45
The update to GNOME 45 was a bit more complex than previous ones. This version of the shell and gjs change a lot of things, so the migration it's not just to add a new number to the metadata.json, but requires incompatible changes, so extensions that works for GNOME 45 won't work for previous versions and vice versa.
But the people working in gnome-shell does a great work documenting and there's a really nice guide about how to upgrade your extension.
The most important part is the import section, that now it has a different syntax.
// Before GNOME 45
const Main = imports.ui.main;
// GNOME 45
import * as Main from 'resource:///org/gnome/shell/ui/main.js';
And some changes in the extension class, that now can inherit from existing ones to provide common usage, like preferences window:
import Adw from 'gi://Adw';
import {ExtensionPreferences, gettext as _} from 'resource:///org/gnome/Shell/Extensions/js/extensions/prefs.js';
export default class MyExtensionPreferences extends ExtensionPreferences {
fillPreferencesWindow(window) {
window._settings = this.getSettings();
const page = new Adw.PreferencesPage();
const group = new Adw.PreferencesGroup({
title: _('Group Title'),
});
page.add(group);
window.add(page);
}
}


Extracting postfix journal logs for fun, profit and unbanning
From journal to .json
In order to convert from your journal log to json, so it is easily parseable, jq offers an option that allows you to run a filter, only until the end of the file:
Instead of running the filter for each JSON object in the input, read the entire input stream into a large array and
run the filter just once.
This allows you to save the file directly, ready to be processed by your favorite tools, here’s what I used:
journalctl -u postfix.service --since yesterday -g "denied" --output json | jq -s "." > data/log.json
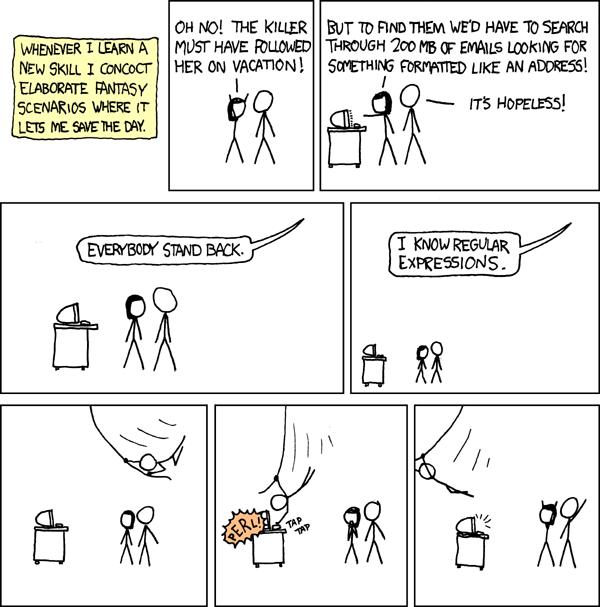
Enter Perl
Now, because I’ve been using Perl for ${deity} knows how long (I wrote my first Perl script at the end of the 90’s),
naturally, is my language of choice for quick things where my knowledge of bash isn’t going to cut it:
First I want to load my file, I’m going to rely on Mojo, specifically
Mojo::Collection and Mojo::JSON for this as I’m familiar with both, also, if I wan’t to dig a bit into what’s inside
my collections, I can always do:
use Mojo::Util qw(dumper);
say dumper $collection->to_array;
But I digress, back to business
The real stuff
This piece of code filters for me, what it reads from a file (I’m doing $_= path(shift); for convenience)
my $file = Mojo::Collection->new(decode_json($_->slurp))->flatten;
// Filter using Mojo::Collection::grep to have a new collection with the data I'm interested in
my $filtered = $file->grep(sub{
$_->{MESSAGE} =~ /denied/
});
Now that I have the elements on a single array (of course, if I’m looking at a file over a gigabyte, likely I’d look into putting this inside some sort of database, PostgreSQL for instance, has excellent Json support), it’s time to do something with it:
// get anything that looks like a hostname before, and get the ip address
// example: NOQUEUE: reject: RCPT from ns2.pads.ufrj.br[146.164.48.5]: 554 5.7.1 <relaytest@antispam-ufrj.pads.ufrj.br>:
// I want to have ethe IP in a named group so I can later reference it with `$+{'IP'}`
my $regexp = qr{(.*[a-zA-Z0-9-._]+)\[(?<IP>.*)\]>?:.*};
Ideally (and for the future) I might want to filter in a different way, and capture different things, but you get the idea however today, we only want to know which ip addresses were rejected while testing our changes in our postfix’s configuration
$filtered->each(sub{
if ($_->{'MESSAGE'} =~ /$regexp/ ){
say "bash ./unban ".$+{'IP'};
} else {
warn "CANNOT GET IP: ".$_->{"MESSAGE"};
}
});
I have another script that does the unban, but for now I’m ok with copy&pasting :)
The full script is at foursixnine/stunning-octo-chainsaw pull requests are welcome, and maybe in the future I move this to its own thing, but for now, that’s all folks.


Notifications About Failed SCM/CI Workflows and More


Prospect Mail | Best Microsoft Outlook Experience on openSUSE


openSUSE Tumbleweed – Review of the week 2023/43
Dear Tumbleweed users and hackers,
Another week fully loaded with Tumbleweed snapshot comes to an end. This week, we have delivered five snapshots (with a new one already in openQA).
The five snapshots (1019, 1020, 1022, 1023, and 1025) brought you those changes:
- KDE Frameworks 5.111.0
- KDE Plasma 5.27.9
- Samba 4.19.2
- SQLite 3.43.2
- Apache 2.4.58
- Linux kernel 6.5.8
- Pipewire 0.3.83
- Virtualbox 7.0.12
- zlib 1.3
- Redis 7.2.2
- Meson 1.2.3
And, as after the snapshot is before the snapshot, the subsequent things are already lined up and getting ready to reach you. The most intriguing things there are:
- Qemu 8.1.2
- VLC 3.0.19
- LLVM 17.0.3
- systemd: Ship the main configuration files in /usr/lib/; this change will hopefully encourage users to customize the defaults via drop-ins, hence removing the risk of conflicts with downstream customization.
- Boost 1.83.0
- Linux kernel 6.5.9
- openSSL 3.1.4
- PHP 8.2.12
- binutils 2.41
- moving to dbus-broker


Security Issues in Passim Local Caching Server
This is a report about findings in the Passim local caching server.
1) Introduction
Passim is a relatively new project for a local caching server that helps distributing publicly available files in local networks to save network bandwidth. It is a dependency of new fwupd releases, which is why it has come to our attention.
Passim consists of a daemon component running as a separate passim user and group. The daemon offers a local D-Bus interface over which only the root user may publish or unpublish files on the network. Non-root users may only inspect the available items via D-Bus.
Furthermore the daemon announces all cached items via the Ahavi discovery protocol. For retrieval of individual items a small libsoup based HTTP server is integrated into the daemon, listening on port 25000.
A small command line programm passim allows to interact with the
daemon’s D-Bus interface.
The findings in this report are based on the upstream release tag 0.1.3.
2) Findings
2.1) Remote DoS Against passimd by Triggering NULL Pointer Dereference
When accessing a URL different from the root “/” and without passing any parameters “?” then a segmentation fault is the result in passim-server.c:751 (null pointer dereference, because there is no request).
Example:
root# curl -v -k 'https://localhost:27500/myfile'
root# journalctl -u passim.service | tail -n 5
Oct 25 12:45:24 mybox passimd[5091]: accepting HTTP/1.1 GET /myfile from ::1:39278 (loopback)
Oct 25 12:45:24 mybox passimd[5091]: g_strsplit: assertion 'string != NULL' failed
Oct 25 12:45:29 mybox systemd[1]: passim.service: Main process exited, code=dumped, status=11/SEGV
Oct 25 12:45:29 mybox systemd[1]: passim.service: Failed with result 'core-dump'.
Upstream has library settings in effect to abort on failing assertions instead of trying to continue, to prevent possible memory access errors from becoming exploitable.
This issue is fixed via upstream commit 1f7bcea.
2.2) Serving Static Files from a Directory owned by Unprivileged Users
Passim supports the configuration of static directories on the local file system, whose content will be processed and published upon startup.
Consider a directory controlled by ‘nobody’:
root# cat /etc/passim.d/nobody.conf
[passim]
Path=/var/lib/nobody/passim
There’s two things that I found problematic in such a scenario.
a) Placing Inaccessible Files in the Directory
root# sudo -u nobody -g nobody /bin/bash
nobody$ mkdir /var/lib/nobody/passim
nobody$ touch /var/lib/nobody/passim/somefile
nobody$ chmod 000 /var/lib/nobody/passim/somefile
This will prevent future starts of passimd:
root# systemctl restart passim.service
Job for passim.service failed because the control process exited with error code.
See "systemctl status passim.service" and "journalctl -xeu passim.service" for details.
root# journalctl -u passim.service | tail -n 6
Oct 25 12:56:58 mybox passimd[5330]: scanning /var/lib/nobody/passim
Oct 25 12:56:58 mybox passimd[5330]: failed to scan sysconfpkg directory: Error opening file /var/lib/nobody/passim/somefile: Permission denied
Oct 25 12:56:58 mybox systemd[1]: passim.service: Main process exited, code=exited, status=1/FAILURE
Oct 25 12:56:58 mybox systemd[1]: passim.service: Failed with result 'exit-code'.
Oct 25 12:56:58 mybox systemd[1]: Failed to start Local Caching Server.
This opens a local DoS attack vector against passimd for the unprivileged user
that owns the directory. This is also valid for other situations like a FIFO
placed there, broken symlinks or symlinks to inaccessible locations as well as
race conditions (time of readdir() vs. time of open()).
This has at least partially been addressed by upstream commit f4c34bd3.
b) Placing Symlinks to Otherwise Inaccessible Data in the Directory
Although passimd runs with low privileges by default there are some
interesting files that a local attacker might want to get their hands
on. Since passimd follows symlinks in this directory one could try to
“publish” files from /proc/<pidof passimd> by placing symlinks. This is
somewhat difficult though, since a race condition has to be won (the PID
of a starting passimd needs to be known to place a proper symlink).
Also there are not that many interesting files in there I believe. Also e.g.
/proc/<pid>/mem cannot be shared this way, since it cannot be read
sequentially.
A much simpler attack is to publish the SSL private key of passimd though:
root# sudo -u nobody -g nobody /bin/bash
nobody$ mkdir /var/lib/nobody/passim
nobody$ ln -s /var/lib/passim/secret.key /var/lib/nobody/passim/secret
root# systemctl restart passim.service
root# passim dump
passimd is running
1c69e7e4d7b7ed655eafa94942a5ef04f7c7688a0519be387133176154f58fe6 secret size:2.5 kB
root# sha256sum /var/lib/passim/secret.key
1c69e7e4d7b7ed655eafa94942a5ef04f7c7688a0519be387133176154f58fe6 /var/lib/passim/secret.key
From here on the local attacker can simply download the now shared “secret key” from localhost.
It has to be noted that this SSL private key has no security purpose in passimd but only serves to prevent network traffic security scanners from raising alarm over unencrypted traffic.
Thus currently there is no known information leak using this attack that has attacker value. It is still crossing of a security boundary and could be problematic in the future.
Upstream issue #26 deals with this issue but is not yet completely fixed, due to a remaining race condition.
Bugfix Release and Upstream Reporting
I reported these issues to the upstream author on 2023-10-25. No coordinated disclosure was desired so bugfixes have been and still are developed publicly over the GitHub issue tracker.
There are some disagreements with upstream about whether these issues are qualifying as security issues. I believe they are. Due to this no CVEs have been assigned as of now.
Passim is packaged, to my knowledge, in Fedora Linux and Arch Linux already. Otherwise it should not be widespread.
Upstream is working on a new release of Passim containing fixes for these and some other non-security issues that I reported as well.
References


File Descriptor Hijack vulnerability in open-vm-tools (CVE-2023-34059)
Introduction
During a routine review of the setuid-root binary
vmware-user-suid-wrapper from the open-vm-tools repository I
discovered the vulnerability described in this report. The version under
review was open-vm-tools version 12.2.0. The setuid-root binary’s source
code in the open-vm-tools repository did not change since version 10.3.0
(released in 2018), however, so likely most current installations of
open-vm-tools are affected by this finding.
Behaviour of vmware-user-suid-wrapper
On first look the vmware-user-suid-wrapper seems to be small and harmless:
- it opens /dev/uinput as root, if it believes to be running on Wayland.
The latter is determined by inspecting the value of the environment
variable
XDG_SESSION_TYPE, checking whether it is set to “wayland”. - it opens /var/run/vmblock-fuse/dev, if existing, as
root. - it permanently drops all privileges to the real (unprivileged) user and group ids and executes /usr/bin/vmtoolsd, inheriting to it any of the previously opened file descriptors.
- the new
vmtoolsdprocess will inspect the environment, e.g. check whether the current host is running in a vmware guest environment and whether a graphical session is available. If one of these is not fulfilled then the process quickly terminates. On success the daemon keeps running, providing its services, keeping the privileged file descriptors open.
So it seems everything is in order, the program opens up to two
privileged files, drops privileges and passes the open files on to
vmtoolsd to use them in the calling user’s context.
The Vulnerability
The (somewhat surprising) problem here is the combination of dropping
privileges to the real uid / gid and the following execve() to execute
the non-setuid program vmtoolsd. During the execve() the process’s
“dumpable” attribute is reset to the value of 1.
From the man page prctl(5) we can learn the following about a
process’s dumpable attribute:
Normally, the "dumpable" attribute is set to 1. However, it is reset to
the current value contained in the file /proc/sys/fs/suid_dumpable (which by
default has the value 0), in the following circumstances:
[...]
- The process executes (execve(2)) a set-user-ID or set-group-ID program,
resulting in a change of either the effective user ID or the effective
group ID.
[...]
Processes that are not dumpable can not be attached via ptrace(2)
PTRACE_ATTACH; see ptrace(2) for further details.
On most Linux distributions the global suid_dumpable setting is set
either to 0 (setuid programs may not dump core at all) or 2 (setuid
programs may dump core but only in safe file system locations).
Consequently when vmware-user-suid-wrapper runs, its dumpable
attribute is set to 2 on openSUSE Tumbleweed, which I have been using
while researching this issue. However after the execve() this changes,
as is also documented in the execve(2) man page:
The following Linux-specific process attributes are also not preserved
during an execve():
- The process's "dumpable" attribute is set to the value 1, unless a
set-user-ID program, a set-group-ID program, or a program with
capabilities is being executed, [...].
Consequently when vmtoolsd is executed with dropped privileges, the
process’s “dumpable” attribute will be reset to 1.
The problem with this is that the unprivileged user that originally
invoked vmware-user-suid-wrapper now is allowed to ptrace() the
vmtoolsd process along with a number of other operations that have not
been allowed on the setuid-root process before.
The interesting resources that vmtoolsd has from a unprivileged user’s
perspective are the open file descriptors for /dev/uinput and/or
/var/run/vmblock-fuse/dev. With the help of ptrace() malicious code
could be injected into the vmtoolsd process to get access to the
privileged file descriptors. An even easier approach is to use modern
Linux’s pidfd API pidfd_open() and pidfd_getfd() to obtain a copy of
the privileged file descriptors. In the man page pidfd_getfd(2) we can
find:
Permission to duplicate another process's file descriptor is governed by a
ptrace access mode PTRACE_MODE_ATTACH_REALCREDS check (see ptrace(2)).
In this context this again boils down to the process’s “dumpable” attribute which is now set to 1, and thus the operation is allowed.
Exploiting the Issue
vmware-user-suid-wrapper can be forced to open /dev/uinput even if not
running on Wayland by setting the user controlled environment variable
XDG_SESSION_TYPE=wayland. This means the file descriptor for this
device file will always be a valid attacker target independently of the
actual situation on a system.
There are two different scenarios to look at regarding the
exploitability of the issue. The easier case is when a valid environment
for vmtoolsd is available i.e. a graphical desktop session is existing
and the check for running in a VMware guest machine is succeeding
(function call VMCheck_IsVirtualWorld()). In this case vmtoolsd will
continue running permanently and there is no race condition to be won.
Exploiting the issue is straightforward, as is demonstrated in the
PoC program vmware-get-fd.c.
The more difficult case is when an attacker is either not running a
graphical environment or not even running in a VMware guest environment.
In the worst case vmtoolsd will terminate quickly, because of the
failing VMCheck_IsVirtualWorld() check. Thus the time window for
actually operating on the vulnerable process is short. A variant of the
PoC program, vmware-race-fd.c, starts the
vmware-user-suid-wrapper continuously and attempts to snatch the
privileged file descriptors from the short-lived vmtoolsd process. In
my tests this often succeeded quickly (even on the first attempt),
likely when the vmtoolsd resources have not yet been cached by the
kernel. Later attempts often take a longer time to succeed but still
succeeded after 10 to 20 seconds.
In summary the existence of the setuid-root program
vmware-user-suid-wrapper is enough to exploit the issue for
/dev/uinput. The attacker needs no special permissions (even the
nobody user can exploit it) and the operating system doesn’t even need
to be running as a VMware guest. This can be relevant in situations when
open-vm-tools are distributed by default in generic Linux distributions
/ images, or in environments where unprivileged users are allowed to
install additional software from trusted sources without root
authentication (a model that is e.g. supported by the PackageKit
project).
Vulnerability Impact
/dev/uinput
Getting access to a file descriptor for the /dev/uinput device allows an attacker to create arbitrary userspace based input devices and register them with the kernel. This includes the possibility to send synthesized key or mouse events to the kernel. The example program uinput-inject.c demonstrates how this can be used to cause arbitrary key strokes to be injected into local user sessions both graphical or on textual login consoles. Thus this attack vector borders the area of arbitrary code execution with the restriction that a local interactive user needs to be present.
This aspect of the vulnerability could be used to increase privileges after gaining low privilege access e.g. through a remote security hole. On multi user machines with shared access it could be used to prepare an attack where a background process waits for a victim user to log into the machine and then inject malicious input into its session.
Since /dev/uinput is not VMware specific, this attack vector is basically also available in non-VMware environments.
The following is an example exploit run using the attached programs, provided
the vmware-user-suid-wrapper is already installed and a compiler is
available:
user$ gcc -O2 vmware-race-fd.c -ovmware-race-fd
user$ gcc -O2 uinput-inject.c -ouinput-inject
user$ ./vmware-race-fd
vmware-user: could not open /proc/fs/vmblock/dev
vmware-user: could not open /proc/fs/vmblock/dev
[...]
/usr/bin/vmtoolsd running at 12226
Found fd 3 for /dev/uinput in /usr/bin/vmtoolsd
Executing sub shell which will inherit the snatched file descriptor 4 (check /proc/self/fd)
user$ ls -l /proc/self/fd/4
l-wx------ 1 user group 64 Jul 25 13:43 /proc/self/fd/4 -> /dev/uinput
user$ ./uinput-inject 4
Sleeping 3 seconds for input subsystem to settle
completed one iteration
completed one iteration
This will continuously write the line “you have been hacked” onto whatever session is currently selected on the system’s display.
/var/run/vmblock-fuse/dev
As far as I understand, this file is created by the vmware-vmblock-fuse
daemon and represents a control file. The FUSE file system is used to
implement access to folders shared between the VMware host and VMware guests.
This file allows, according to documentation, to add, delete or list
blocks in shared folders.
As a result access to this file descriptor breaks the boundary between different users in the guest system regarding shared folder access. The integrity of the shared folder content can be violated. It might also be possible to leak information from shared folders into the unprivileged user’s context.
Depending on the actual environment it might allow to result in code execution if e.g. malicious code is written to shared folders that could then be executed even on the VMware host system.
The vmware-fuse documentation mentions the outlook to allow unprivileged users access to this control file, but this idea seems not safe to me in its current form.
I did not look more closely into practical exploits of this.
Suggested Fix
To fix this problem it must be prevented that the “dumpable” attribute
of the vmware-user-suid-wrapper process is reset when executing
vmtoolsd. One way to achieve this could be to move the privilege drop
logic into vmtoolsd instead. As long as the process is running in the
setuid-root context, the “dumpable” attribute will not be reset.
vmtoolsd can then drop privileges and also mark the privileged file
descriptors with the O_CLOEXEC flag to prevent them to be inherited
unintendedly to further child processes, which might result in the same
problem again.
Update: This is the route that the patch provided by upstream has taken.
As a first aid and/or hardening measure, access to the
vmware-user-suid-wrapper could be limited to members of a privileged
group e.g. vmware-users. This would reduce the attack surface and
prevent e.g. a compromised nobody user account to exploit this.
In terms of hardening, the vmware-user-suid-wrapper could also add
some code to sanitize the environment variables passed from the
unprivileged context, which is a frequent source of security issues in
setuid-root binaries. At least the PATH variable should be reset to a
safe value to avoid any future surprises when looking up executable for
execve().
Timeline
| 2023-07-25 | I reported the findings to security@vmware.com, offering coordinated disclosure |
| 2023-08-23 | VMware security asked for a publication date in early November exceeding our maximum 90 days disclosure policy. We reluctantly agreed to this exception. |
| 2023-10-20 | VMware shared the issue and bugfixes with the distros mailing list without keeping me in the loop. In parallel an earlier publication of 2023-10-26 has now been communicated to me. My requests to get a draft patch for review before publication have not been honored. |
| 2023-10-27 | The general publication date has been reached. |
References


Apache, Plasma, firewalld updates in Tumbleweed
This week saw a major transition in openSUSE Tumbleweed for YaST as it moved to a new major version.
Several other packages like Apache, Redis, GVfs, Vim, KDE Plasma 5.27.9 and Frameworks updated in the rolling release this week.
KDE Plasma 5.27.9 arrives in snapshot 20231025. The latest update for the Plasma Desktop makes implements changes to avoid recursively adding every copied file to the desktop. Its recent files component ensures compatibility with an older Frameworks version of kconfigwidgets. Kwin resolves a misgenerated QHoverEvent and enhances functionality by adding QKeySequence functionality to a part of the Virtual Desktop Manager. An update of firewalld 2.0.1 resolves issues related to the command-line interface (CLI) by ensuring that the --list-all-zones output is consistent and that the default zone attribute is correctly displayed. Active attributes for zones and policies are shown accurately, and the --get-active-zones command includes the default zone. There were also enhancements in the nftables integration, so the main table is now always flushed upon the start. Several other issues were resolved, including the proper usage of IPv6 names for ICMPv6 and the configuration of IP ranges and values for ipsets when working with nftables. Updates for GNOME users also arrived in the snapshot. An update of gnome-control-center 45.1 includes enhancing the ability to close the Cursor Size and Shortcuts dialogs using the Escape key. It also supports more types of processors in the About section. A lower timeout when downloading service files, which leads to improved performance was made in the gnome-maps 45.1. This snapshot also updates gnome-terminal to version 3.50.1, which has checks for alternate terminals within the Flatpak environment and improves the handling of the headerbar preference. The second kernel-firmware of the month to version 20231019 fixes the robot email script, updates AMD CPU microcode and introduces support for sending emails during PR/patch processing. The 7.2.2 version of redis has a critical Common Vulnerability and Exposure fix; CVE-2023-45145 creates a race condition that potentially leads to unauthorized Unix socket permissions upon startup, which had existed since the 2.6.0 release candidate version. Several more packages were updated in the snapshot.
Snapshot 20231023 brought updates of some GNOME packages like gvfs, evolution and gnome-software 45.1. The latter update brings various styling fixes, an ability to report PackageKit GPG-related errors in the graphical user interface and it improves Flatpak permission checks. The update also includes translation updates. With evolution 3.50.1, the personal information management application fixes bugs like correcting the conversion of UTF-16 encoded text files, enabling spell checking for editable fields and updates default calendar colors. A fix warning about the failure to solve a puzzle when loading games was made in the gnome-sudoku 45.2 update. Another GNOME package to update was gvfs 1.52.1. This Virtual filesystem implementation addresses issues including the prevention of returning invalid mount cache entries in the client, fixes authentication problems when using DNS-Service Discovery Uniform Resource Identifiers (URI) and resolves IPv6 URI handling problems in the Network File System component. An update of harfbuzz 8.2.2 fixes a regression from 8.1.0 in shaping fonts with duplicate feature tags and resolves a regression from in parsing CSS-style feature strings. The update ofvirtualbox 7.0.12 addresses multiple CVEs like CVE-2023-22098, CVE-2023-22099 and CVE-2023-22100, which would lead to can lead to unauthorized access and system crashes. Several other packages were updated in the snapshot including rubygem-agama 5, which has enhancements like not reusing pre-existing swap partitions in the storage proposal, extends the Software service to configure selected patterns and adapts storage settings for ALP Dolomite.
The update of apache2 2.4.58 arrives in snapshot 20231022. Apache2 addresses CVE-2023-45802, which relates to stream memory management, and CVE-2023-43622, which addresses a DoS vulnerability. The updates include various improvements like enhanced support for WebSockets via HTTP/2 and the introduction of new directives for better control and logging in various scenarios. A 16.2.14.66 update of ceph takes care of issues related to minimal file system BlueFS and enables a 4K allocation unit for it. The package also enables building for RISC-V. An update of dracut addresses issues related to FIPS (Federal Information Processing Standards) setup that was causing test failures and core dumps in various test scenarios. An update of the Linux Kernel had enhancements for Advanced Linux Sound Architecture among other things. The kernel-source 6.5.8 package has network-related component changes, such as net drivers and protocols, and addresses other issues with audio and sound support like that of ALSA System on Chip for a non-functioning mic on Lenovo 82YM. An update of pipewire 0.3.83 fixes a regression, reduces memory usage in audio conversion and removes the buffer-size limit with JACK. The update of xfce4-terminal 1.1.1 improves X11 and Wayland compatibility. Among the other packages to update were libstorage-ng 4.5.149, yast2-storage-ng 5.0.3, freerdp 2.11.2 and more.
The update of the man package 2.12.0 in snapshot 20231020 addresses manual page portability issues and enables timestamps beyond 2038 for the Y2K38 event that’s a long time away.An update of nftables 1.0.9 introduces improvements like custom conntrack timeouts and better support for dynamic sets. Plus it fixes a crash with a log prefix longer than 127 bytes. The sqlite3 3.43.2 update fixes memory leaks, and enhances the JSON processing performance. The version also adds support for Full-Text Search version 5 (FTS5) Indexes that allows for the deletion of indexed records without retaining the content of the deleted records. A ton of version 5 packages in the snapshot align YaST’s versioning with SUSE versions and the service packs it supports; more than 50 yast2 packages transitioned to version 5 to align with one of SUSE’s next major releases.
KDE Plasma users who did a zypper dup with snapshot 20231019 and later received KDE Frameworks 5.111.0 updates. The KIO made improvements to dbusactivationrunner’s service activation and fixes some object paths. A fix in Kirigami allows customizing ‘donateUrl’ in AboutPage for Donate button removal. KImageFormats brings support for repetition count in the avif format, has fixes for multi-image loading in the raw format, and resolves various issues, including crashes in the High Dynamic Rang and Gimp’s xcf formats. The libnvme 1.6+5 update fixes an issue by avoiding stack corruption caused by unaligned direct memory access to user space buffers, as reported. The regular expressions library oniguruma updates to version 6.9.9 in the snapshot. This update includes updating Unicode to version 15.1.0, introducing a new API called and, addressing issues related to character classes and POSIX brackets. Rendering library virglrenderer had its first major release with version 1.0.0. The update transitions to the Venus protocol, eliminating the experimental label from the Venus configuration option. This release also improves the handling of fences between guest and host for synchronization purposes. More major versions of YaST 5 arrived and there were a few other updates to include a 4.19.2 version of samba.
Only three packages updated in snapshot 20231018 from last week that did not make it in our weekly review. That update includes enhancements and improvements to the kernel module management tools kmod; version 31 includes in-kernel decompression for performance and depmod now supports a separate output directory. Another package to update was python-pytz 2023.3.post1 that is replacing deprecated datetime.utcfromtimestamp() and is adding support for Python 3.12. Text editor vim 9.0.2043 was also in the snapshot and enhances documentation, translations and provides a few fixes.

 Member
Member foursixnine
foursixnine


