

How can one catch OS X sandbox violations in a debugger?
Do you know of any way to catch OS X sandbox violations as they happen (in a huge program like LibreOffice where you don't have a clue what is going on in all places in the codebase) in a debugger (either gdb on the command line, or lldb under Xcode)? The trick using Dtrace in https://devforums.apple.com/message/874181#874181 does not seem to work in 10.9.1 at least.


FOSDEM14 lima driver talk.
Luckily, some people from the sunxi community took the livestream of sunxi related talks, and produced some quick dumps of it. I have now copied the Mali driver talk over to my fd.o account so that the sunxi server doesn't become too overloaded. Slides are also available.
This talk mentions where i am at with my mesa driver, why i am taking the route i am taking, the importance of SoC communities, and how the lack thereof hampers driver development, and also talks about the company ARM and their stance towards the open driver.
Enjoy!


First fruits – update on openQA and Staging work
In our previous summary, we talked about some basic research and some ground work to build on. This time we have some first exciting results!
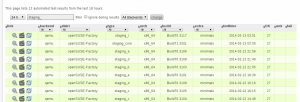
openQA
Last week we rearranged the repository a little bit, creating a new branch called "devel" where all the exciting (and not so exciting) changes are taking place. Our little Factory 
The main difference between this branch as master is that, as you could read in the previous blog, the devel branch is openQA build on Mojolicious, a nice web development framework. And having a proper web framework is starting to show its benefits: we have openID login available! Unfortunately the current openSUSE openID provider is a little bit weird, so it doesn’t play well with our tool yet, but some others are working and openSUSE accounts will be the next step. Having working user accounts is necessary to be able to start defining permissions and to make openQA truly multiuser. And to be able to deploy the new version on a public server!
The other main focus of this week has been internal polishing. We have revamped the database layout and changed the way in which the different openQA components communicate with each other. The openQA functionality is spread out over several parts: the workers are responsible of actually executing the tests in virtual machines reporting the result after every execution; some client utilities are used to load new ISO images and similar tasks and, finally, we have the one openQA Server to rule them all. Until now, the communication between the server and the other components was done using JSON-RPC (a lightweight alternative to XML-RPC). We have dropped JSON-RPC in favor of a REST-like API with just JSON over plain HTTP. This change allowed us to implement exactly the same functionality in a way that is simpler, perfectly supported by any web framework, natively spoken by browsers and easier to authenticate (using, for example, plain HTTP authentication or openID). This is also the first step to future integration with other services (think OBS, as the ultimate goal is to use openQA to test staging projects).
But, who tests the tester? openQA is growing and changing quite fast so we have continued with the task of creating a good testing infrastructure to tests openQA itself to make sure that all our changes do not result in breakage. We only have a few tests right now, but we now have a solid foundation to write more and more tests.
Staging and package manipulation
In the last blog post we told you we were investigating a code test suite to test the abilities of a osc plugin we are writing. osc is the commandline tool for handling the Open Build Service, and this plugin is meant to help with the administration of staging projects. We’ve been thinking about how to move forward with the testing part as we want to make sure the functionality works as advertised. More important, we write tests to make sure that our additions and changes do not break existing functionality. We have started merging functionality from various scripts handling staging thingies and rings we had into this plugin. This is partially done so we can do basic staging project tasks! We can take a request (be it submit or delete) and put it to test in a staging project. We can also move packages between staging projects and we have a simple YAML in project descriptions to indicate what packages and what requests are there.
Coolo already started using the plugin for some tasks, so you can see pretty titles and metadata in staging projects descriptions. Not impressive enough? Let me provide you a good headline:
Thanks to staging projects, no single regression have been introduced this year in the core of Factory
You can enjoy a more detailed description in this announcement written by coolo to the Factory mailing list and have some visual joy in the included screenshot (genuine pr0n for QA engineers).
Last but not least, we also did some cleanup of the sources in the repo and of course we added more tests (as functionality grows). And there has been work on other parts of the plugin, like taking rings into account.
Result
We already have some useful functionality which we are going to expand and build on. Not that much to show yet, but we are progressing towards our goal. You can follow our progress either in the way of tasks (openQA and staging projects) or just follow our commit history on github (again for both openQA and staging plugin).
We are very much looking forward to feedback and thoughts – these changes aim to make Factory development easier and thus we need to hear from all you!


Gerenciando seu smartphone Android via wifi com Air Droid
Acessar seu smartphone via cabo usb utilizando o protoclo MTP às vezes pode ser uma dor de cabeça. Uso o openSUSE e às vezes o aparelho simplesmente é desconectado mesmo estando com o cabo usb plugado, ou seja é uma chatice só. Passei então a procurar um aplicativo no GooglePlay que pudesse me ajudar nesta tarefa. Encontrei o Samsung Kies (meu celular é um Samsung Trios) com um custo muito baixo (quase R$4,00) e também encontrei um outro aplicativo que me chamou a atenção que foi o Air Droid.
Com o Air Droid instalado, basta eu me conectar na mesma rede wifi que meu smartphone estiver conectado e autorizar a conexão no meu celuar, ou seja, quando inicio o Air Droid ele acessa a rede wifi e me informa um endereço na rede ex: 192.168.1.20:888, então, basta acessar este endereço no meu navegador preferido em meu notebook. Ao acessar este endereço aparece no celular a mensagem de uma conexão que está sendo feita e a pergunta se eu autorizo. Depois de autorizar, consigo acessar todas as funções do meu celular via navegador.
Depois de estabelecida a conexão, eu consigo acessar a lista de contatos, fotos, arquivos, ver e gravar vídeos, músicas, transferir arquivos, efetuar ligações, instalar e remover aplicativos, enviar e gerenciar mensagens SMS e o melhor de tudo sem o maldito cabo USB.
Veja uma imagem da tela:
Você pode configurar o nível de segurança do aplicativo, por exemplo, você pode escolher se deve ser dada permissão ou se a conexão entre computador e smartphone pode acontecer sem que haja essa necessidade. Claro que recomendo que seja necessário autorizar o acesso. Já pensou qualquer pessoa poder acessar seu smartphone ??
Resumindo… achei muito interessante e funcional este aplicativo. Remendo com louvores.
Se estiver interessado em baixar ou saber mais sobre o aplicativo acesse esta página:
https://play.google.com/store/apps/details?id=com.sand.airdroid&hl=pt_BR


openSUSE Board In The Flesh


$ICECC_VERSION
It's been brought to my attention that the Icecream documentation more or less suggests it is necessary to manually set up $ICECC_VERSION (which also involves creating the environment tarball with the compiler and so on). That is incorrect. I've already updated the documentation to say that, like with pretty much everything, Icecream simply figures it out itself by default.
So if you happen to use $ICECC_VERSION, unless you know why you do that (e.g. cross-compilation), don't. It's not only simpler but also better to leave it up to Icecream to package the system compiler as necessary, as it simply works, and avoids possible problems (such as updating the system compiler and forgetting to update the tarball).


Docker and openSUSE getting closer
I have some good news about Docker and openSUSE.
First of all the Docker package has been moved from my personal OBS project to the more official Virtualization one. The next step is to get the Docker package into Factory :)
I’m going to drop the docker package from home:flavio_castelli:docker,
so make sure to subscribe to the Virtualization repository to get latest versions of
Docker.
I have also submitted some openSUSE related documentation to the official Docker project. If you visit the “Getting started” page you will notice the familiar geeko logo. Click it to be redirected to the openSUSE’s installation instructions.


Improved OS X look of the upcoming LibreOffice 4.3
We achieved a lot (incomplete list - many haven't added their achievements yet), but I want to particularly highlight the result of me teaming up with +Joren dc and +Tor Lillqvist. It is the new look of LibreOffice on OS X:
 |
| Improved OS X look of LibreOffice |
Have a look at the toolbar - it is using CoreUI to render the gradient in a native way. It is based on similar work that has been done for Firefox - thank you, Markus Stange, for your observations & code, we have reused pieces under the MPL license.
It is visible that the work is not finished yet; we need to extend the gradient to cover even the title bar (or how is it called exactly?), but there is enough time for the LibreOffice 4.3 feature freeze in May - I am sure it will be perfect by then.
Other Improvements
Other than that, I have extended the new Start Center to be able to show previews of other file formats than just ODF. As a sideeffect, it should improve the startup speed with many previews.The last thing I've done was that I have converted the Template Manager to use dynamic widget layout. This led to removing many hacks there that made the Template Manager resizable even before - but using the .ui is much more elegant, and potentially may allow integration of the Template Manager directly into the Start Center.
Overall, the UX hackfest was awesome - I am really looking forward to the next one :-) Thank you, Mirek, for organizing it!


Instalando somente os updates de segurança no openSUSE 12.3
Quando a gente vai ficando grandinho, só quer que o computador funcione. Especialmente naqueles dias nós precisamos entregar/apresentar um trabalho importante. Portanto, fazer um upgrade do sistema nem sempre é uma boa ideia perto dessas datas.
Uma boa saída no openSUSE é aplicar somente as correções de segurança da base do sistema, deixando para uma época mais tranquila, o update dos demais aplicativos.
Pensando nisso, listei abaixo, fuçado de [1] e [2], os comandos para identificar todos os patches e instalar somente aqueles que são realmente cruciais para o sistema:
Listar todos os patches:
zypper list-patches
Listar somente os patches de segurança:
zypper list-patches –category security
Instalar todos os patches:
zypper patch
Instalar somente os patches de segurança:
zypper patch –category security
Fonte:
[1] – http://forums.opensuse.org/showthread.php/495293-Install-only-the-security-updates
[2] – Manpages do zypper


Some news from the trenches
As you might know, we are focusing our development efforts in two fronts, namely openQA and staging projects. As we just started we don’t have fireworks for you (yet) but we did some solid ground work that we are going to build upon.
Working on openQA
We are organizing our daily job in openQA into highly focused sprints of two weeks. The focus of the first sprint was clear: cleanup the current codebase to empower future development and lower the entry barrier for casual contributors, which can be translated as “cleaning our own mess”. We created some tasks in progress, grouped in a version with a surprising and catchy name: Sprint 01.
Got my mojo workin’
Up to now, openQA web interface was written using just a bunch of custom CGI scripts and some configuration directives in Apache. We missed a convenient way to access to all the bell and whistles of modern web development and some tools to make the code more readable, reliable and easier to extend and test. In short, we missed a proper web development framework. We evaluated the most popular Perl-based alternatives and we finally decided to go for Mojolicious for several reasons:
- It provides all the functionality we demand from a web framework while being lightweight and unbloated.
- It’s stated as a “real time framework” which, buzzwords apart, means that is designed from the ground to fully support Comet (long-polling), EventSource and WebSockets. Very handy technologies for implementing some features in openQA.
- It really “feels” very close to Sinatra, which makes Ruby on Rails developers feel like at home. And we have quite some Rails developers hanging around, don’t we? Just think about OBS, software.o.o, WebYast, progress.o.o, OSEM, the TSP app…
- Mojolicious motto is “web development can be fun again”. Who could resist to that?
We’ve now reached the end of the sprint and we already have something that looks exactly the same than what we had before, but using Mojolicious internally. We are very happy with the framework and we are pretty confident that future development of openQA will be easier and faster than ever. OpenQA has mojo!
The database layer in openQA
Another part that we worked on during first sprint was the database layer. The user interface part of openQA use a SQLite database to store the jobs and workers registered in the system. The connection between the code and the database was expressed directly in SQL using a simple API.
We have replaced this layer with another equivalent that uses an ORM (Object-relational mapping) in Perl (DBIx::Class). Every data model in openQA is now a true object that can be created, copied and moved between the different layers of the application. Quite handy.
To make sure we don’t forget anything, we created a bunch of tests covering the whole functionality of the original code, running this test suite after each step of the migration. In this way we have achieved two goals: we now have a simple way to share and update information through the whole system and we can migrate very easily to a different database engine (something that we plan to do in the future).
What to do with staging
Over the time, coolo had accumulated quite some scripts that helped him with Factory. Most of them are actually related to something we are doing right now: the staging projects. So in the end we basically migrated all relevant ones to github and one by one we are merging their functionality to staging plugin. We also experimented with test frameworks that we could use to test the plugin itself, selected few and we even have a first test! The final plan is to have the whole plugin functionality covered with a proper test suite, so we will know when something breaks. Currently, there is a lot of mess in our repo and the plugin itself need big cleanup, but we are working on it.
Contributions are welcome
If you want to help but wonder where to start, we identified tasks that are good to dive into the topic and named them “easy hacks”: mostly self contained tasks we expect to have little effort but we lack the time to do right now. Just jump over the list for openQA or staging projects.
For grabbing the code related to staging project, you only need to clone the already mentioned repository. The openQA code is spread in several repositories (one, two, three and four), but setting up your own instance to play and hack is a piece of cake using the packages available in OBS (built automatically for every git push).
If you simply want to see what we are doing in more detail, take a look at progress.o.o, we have both openQA and Staging projects there.
We are having a lot of fun, and we encourage you to join us!
 libv
libv
 Member
Member